Feb 24, 2021 | Articles, Hacking Stories
Albert Gonzalez, rose from teenage hacker to orchestrator of one of the largest credit card thefts. In 2007, with the ‘Get Rich or Die Trying’ crew, he used SQL injection to breach data from major companies, accumulating over 50 million credit card accounts.

Jan 18, 2021 | Articles, Malware
The SolarWinds supply chain hack severely impacted the IT infrastructure of both government and large corporate networks. The sophisticated attack exploited SolarWinds’ Orion software, impacting around 18,000 clients globally, including key US departments.
Dec 14, 2020 | Articles
Steganography is the practice of hiding secret messages in otherwise non-secret mediums. It’s different than cryptography where is the idea of encrypting a message…

Nov 16, 2020 | Articles, Hacking Stories
Gary McKinnon, a 36-year-old computer hacker, was accused of hacking into 97 computers belonging to the U.S. Army, Navy, Air Force, Department of Defense, and NASA.
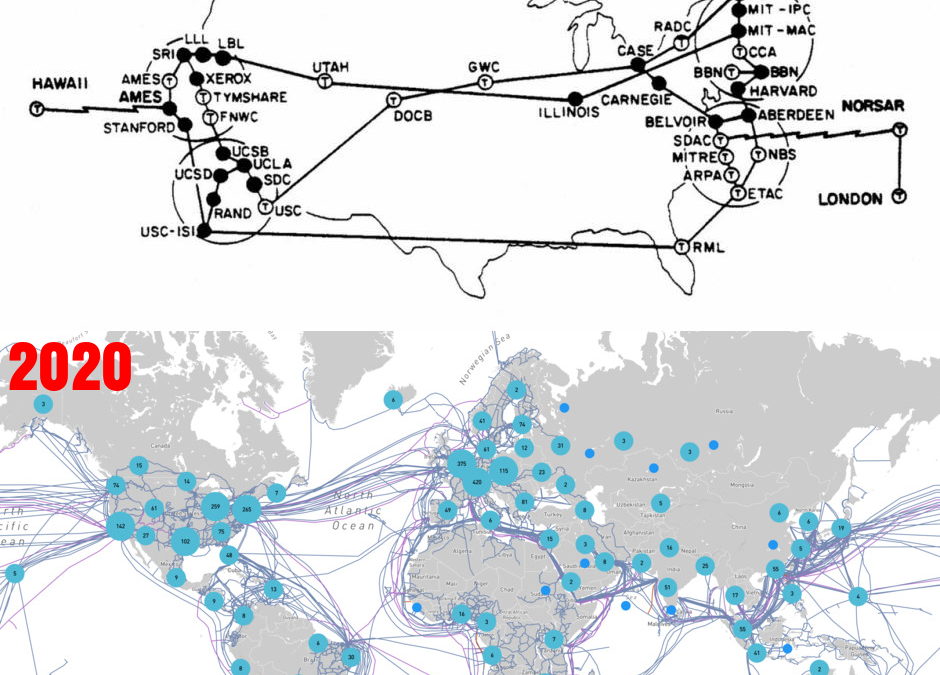
Oct 12, 2020 | Free Access
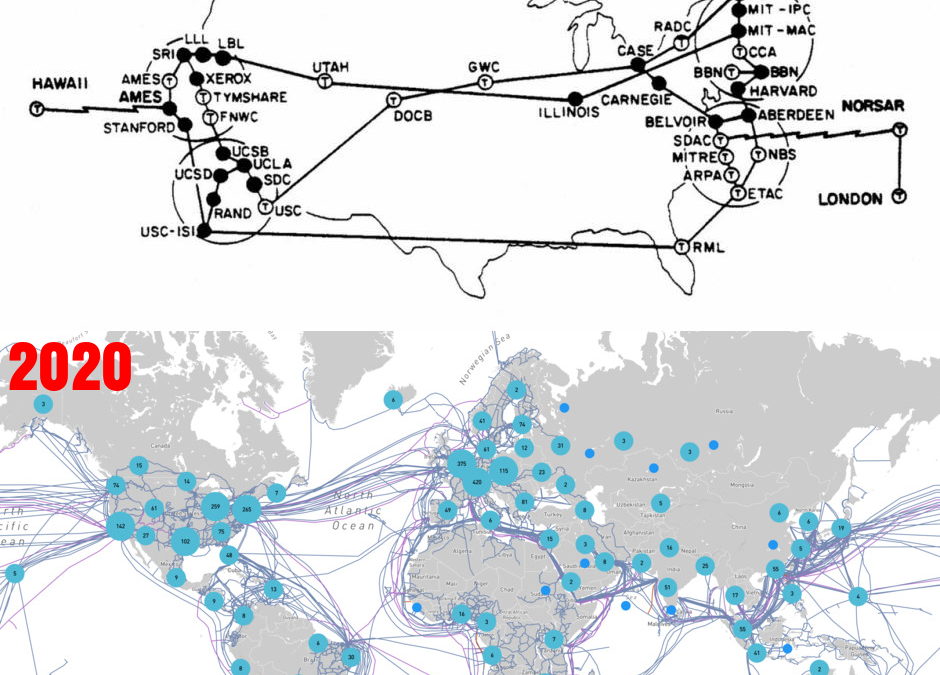
The history of Internet and how it became a worldwide “thing” Post Views: 2,133 style="display:block" data-ad-client="ca-pub-6620833063853657" data-ad-slot="3193330934" data-ad-format="auto" data-full-width-responsive="true" Reading Time: 10...
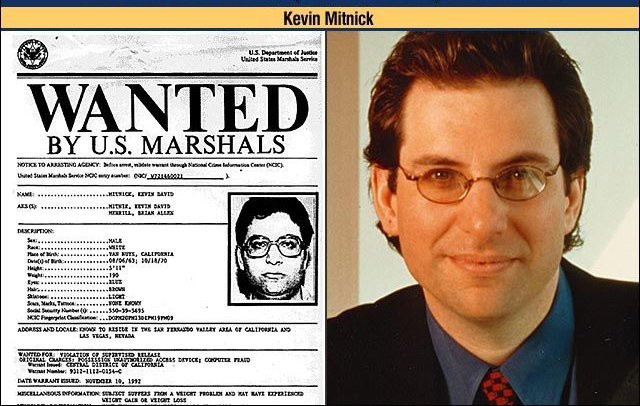
Sep 14, 2020 | Hacking Stories
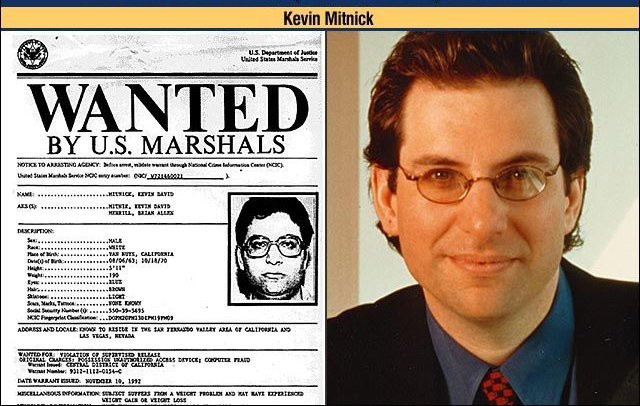
Kevin Mitnick, once called the “Most-Wanted hacker”, is an American security researcher who was born in Los Angeles in 1963.