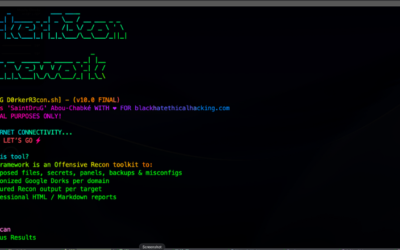
Offensive Security Tool: D0rkerR3con Framework
D0rkerR3con Framework is an offensive reconnaissance toolkit designed to identify exposed files, secrets, administrative panels, backups, and misconfigurations by launching weaponized Google Dorks per domain.
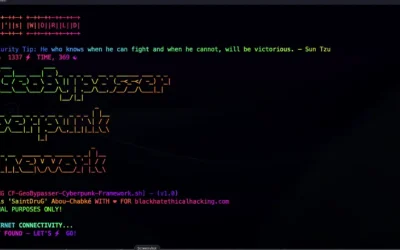
Offensive Security Tool: CF GeoBypasser Cyberpunk Framework
CF GeoBypasser Cyberpunk Framework is a Modular Offensive Toolkit designed to discover and bypass Cloudflare-based Geo-restrictions using country-specific proxies.
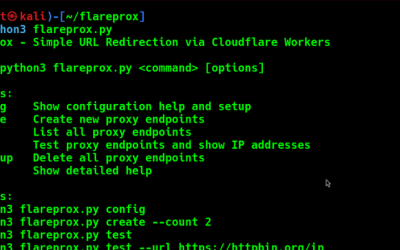
Obfuscation Tool: Flareprox
FlareProx is a tool that deploys serverless HTTP proxy endpoints via Cloudflare Workers, enabling users to redirect web traffic to any destination URL while masking the true origin IP.
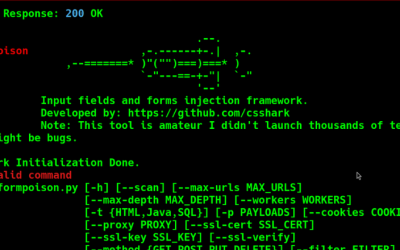
Offensive Security Tool: FormPoison
FormPoison is a form-focused testing framework designed to identify web application vulnerabilities, particularly Cross-Site Scripting (XSS) and SQL injection.
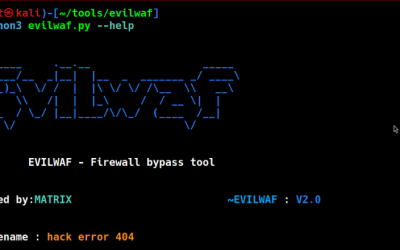
Offensive Security Tool: EvilWAF – Web Application Firewall Bypass Toolkit
EvilWAF is a penetration testing tool designed to detect and bypass common Web Application Firewalls (WAFs).
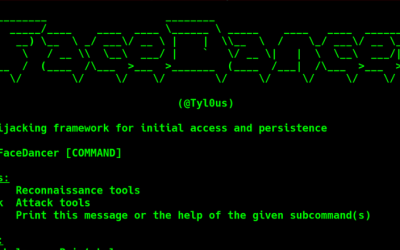
Offensive Security Tool: FaceDancer
FaceDancer is an exploitation tool aimed at creating hijackable, proxy-based DLLs by taking advantage of COM-based system DLL image loading.
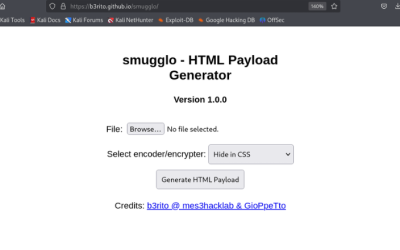
Offensive Security Tool: smugglo
smugglo is an HTML smuggling tool that generates self-contained HTML payloads capable of embedding arbitrary files directly into a browser-renderable HTML document.
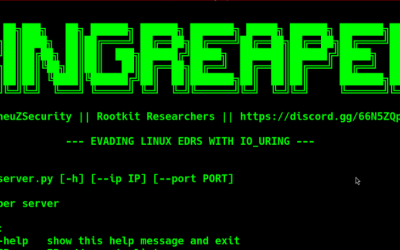
Offensive Security Tool: RingReaper
RingReaper is a stealth-focused post-exploitation agent built for Linux environments, designed to evade Endpoint Detection and Response (EDR) solutions.
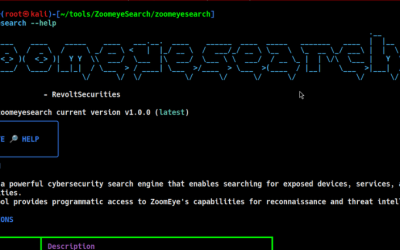
Recon Tool: ZoomeyeSearch
ZoomeyeSearch is a recon tool that provides programmatic access to the ZoomEye cybersecurity search engine. It enables security professionals to search for exposed devices, services, and infrastructure across the internet.