Attackers Impersonate IT Support on Microsoft Teams to Deploy A0Backdoor Malware
Hackers Use Microsoft Teams to Trick Employees Into Granting Remote Access
Threat actors are targeting employees at financial and healthcare organizations by impersonating IT support staff through Microsoft Teams, convincing victims to grant remote access and ultimately deploying a new malware strain called A0Backdoor.
The campaign relies heavily on social engineering. Attackers begin by overwhelming a target’s inbox with spam messages before reaching out through Microsoft Teams, posing as internal IT personnel offering assistance in resolving the issue.
By exploiting the trust employees place in internal support teams, the attackers persuade victims to initiate a remote session using Microsoft’s Quick Assist tool, allowing them direct access to the victim’s system.
Quick Assist Sessions Used to Deliver Malicious Toolset
Once remote access is established, the attackers deploy a malicious toolkit containing digitally signed MSI installers hosted on personal Microsoft cloud storage accounts.
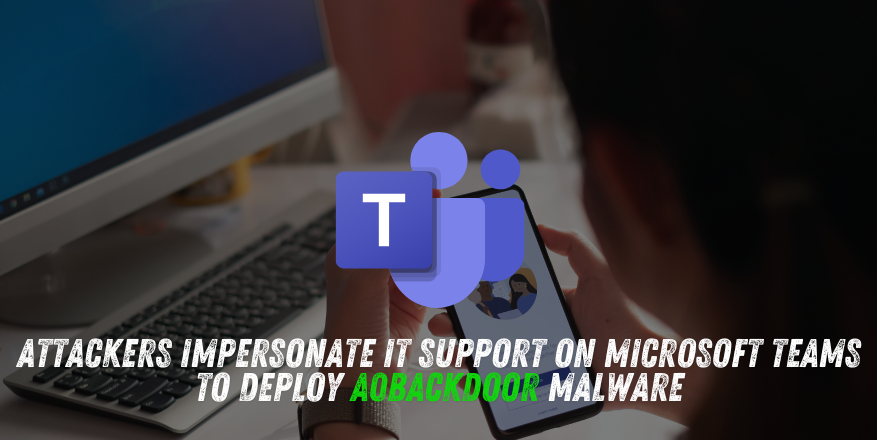
According to researchers at cybersecurity firm BlueVoyant, the installers are designed to appear legitimate by impersonating components related to Microsoft Teams and CrossDeviceService, a genuine Windows service associated with the Phone Link application.
 Command line argument to install the malicious CrossDeviceService.exe
Command line argument to install the malicious CrossDeviceService.exe
Source: BlueVoyant
This disguise helps the attackers evade suspicion while installing the malicious payload on the compromised system.
Offensive Security, Bug Bounty Courses
DLL Sideloading Used to Execute Malicious Code
The attack chain leverages DLL sideloading techniques to execute malicious code using legitimate Microsoft binaries.
During this stage, the attackers deploy a malicious library named hostfxr.dll, which contains compressed or encrypted data. When the DLL is loaded into memory, it decrypts the embedded data into shellcode and transfers execution to it.
Researchers observed that the malicious library uses the CreateThread function extensively as an anti-analysis measure. Excessive thread creation may cause debugging tools to crash, though it does not significantly affect normal execution on infected systems.
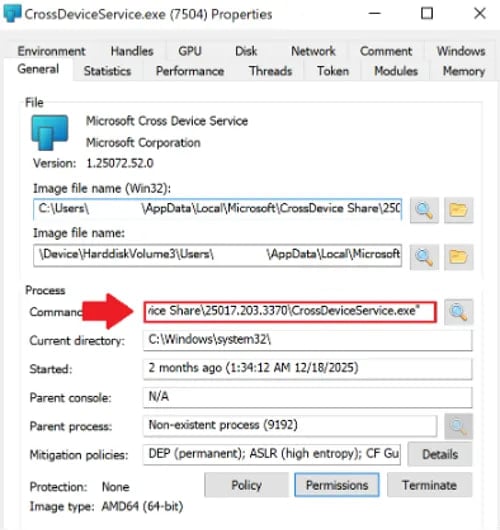
Encrypted Payload Extracts the A0Backdoor
The decrypted shellcode performs several checks to determine whether it is running inside a sandboxed or analysis environment. If the environment appears legitimate, it generates a SHA-256–derived key used to decrypt the final payload.
This payload, the A0Backdoor, is encrypted using the AES algorithm and stored within the shellcode. After extraction, the malware relocates itself to a new memory region and decrypts its core routines before executing them.
The backdoor then collects system information using Windows API functions such as DeviceIoControl, GetUserNameExW, and GetComputerNameW to fingerprint the infected host.
 Encrypted payload in the shellcode
Encrypted payload in the shellcode
Source: BlueVoyant
Command-and-Control Traffic Hidden in DNS Queries
A notable aspect of the malware’s communication mechanism is its use of DNS MX records to hide command-and-control (C2) traffic.
The malware sends DNS queries containing encoded metadata within high-entropy subdomains to public recursive DNS resolvers. The servers respond with MX records that contain encoded commands from the attackers.
According to BlueVoyant, the malware decodes the data embedded in the leftmost DNS label to recover configuration or command instructions before executing them.
Using MX records instead of more commonly monitored DNS record types, such as TXT records, allows the traffic to blend into normal DNS activity and potentially evade detection.
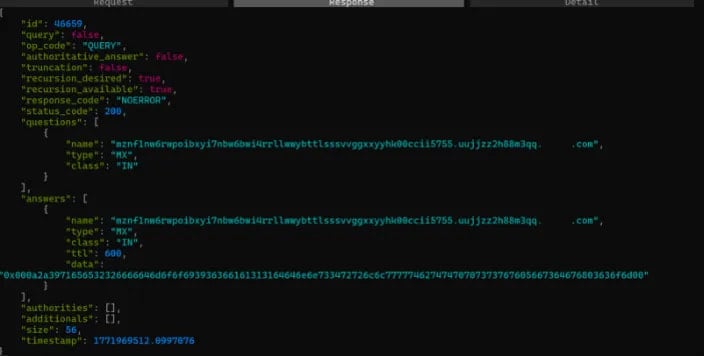 Captured DNS communication
Captured DNS communication
Source: BlueVoyant
Researchers Link Campaign to BlackBasta Tactics
BlueVoyant identified at least two confirmed targets of the campaign, including a financial institution in Canada and a global healthcare organization.
The researchers believe the operation may represent an evolution of tactics associated with the BlackBasta ransomware group, whose operations reportedly collapsed after internal chat logs were leaked.
Although the campaign shares several techniques previously linked to BlackBasta, the researchers note that digitally signed MSI installers, the A0Backdoor malware, and DNS MX-based command-and-control communication represent new elements not previously observed in the group’s attacks.
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Sources: bleepingcomputer.com, bluevoyant.com