EvilTokens Phishing Service Fuels Large-Scale Microsoft 365 Account Takeover Campaign
Large-Scale Device Code Phishing Campaign Targets Microsoft 365 Users
Cybersecurity researchers have uncovered an active and rapidly expanding device code phishing campaign targeting Microsoft 365 accounts across more than 340 organizations worldwide.
The activity, first detected on February 19, 2026, has since accelerated, impacting organizations in the United States, Canada, Australia, New Zealand, and Germany. The campaign spans multiple sectors, including construction, healthcare, financial services, manufacturing, legal, government, and non-profits.
According to Huntress, the operation stands out not only for its scale but also for the diversity of lures and techniques used to compromise victims.
Attackers Combine Multiple Lures to Increase Success Rates
The campaign employs a wide range of social engineering tactics to maximize effectiveness. These include:
- Construction bid requests
- DocuSign impersonation
- Voicemail notifications
- Microsoft Forms abuse
- Automated landing page generation
Despite the varied entry points, all attacks ultimately lead victims into the same credential harvesting infrastructure hosted on Railway, a platform-as-a-service provider.
Researchers also observed the use of Cloudflare Workers redirects and multi-stage redirection chains involving compromised websites and services like Vercel, enabling attackers to bypass traditional email security controls.
How Device Code Phishing Enables Persistent Access
Device code phishing abuses the legitimate OAuth device authorization flow, allowing attackers to obtain persistent access tokens without directly stealing passwords.
The attack unfolds as follows:
- The attacker requests a device code from Microsoft Entra ID using the legitimate API.
- A phishing email is sent, instructing the victim to visit the official Microsoft device login page and enter the provided code.
- The victim authenticates using their credentials and multi-factor authentication (MFA).
- Microsoft issues access and refresh tokens tied to the device code.
- The attacker retrieves these tokens and gains ongoing access to the account.
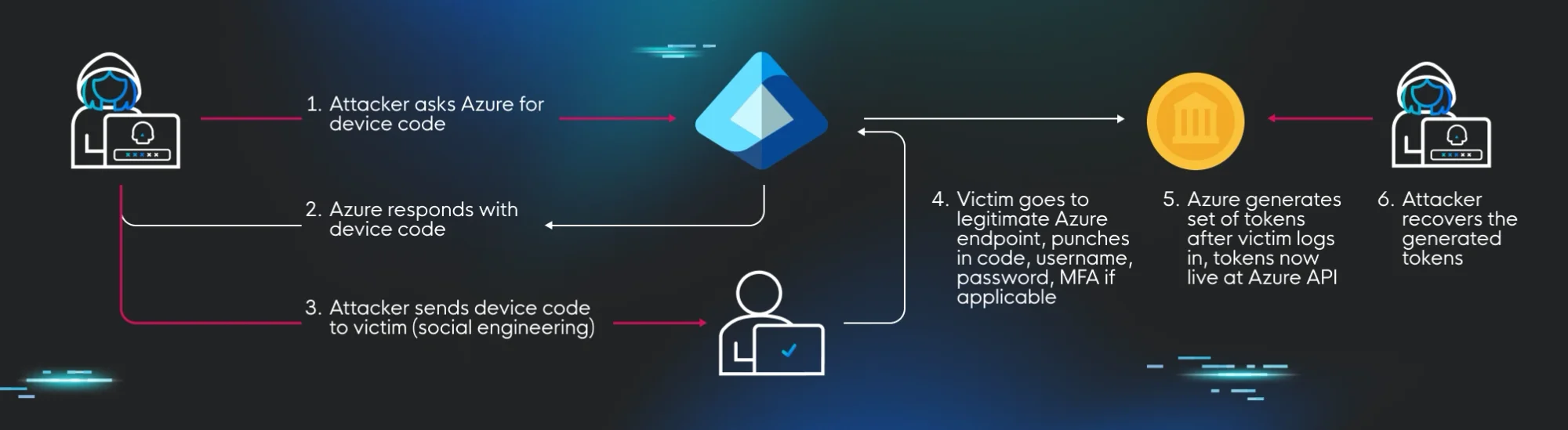
Figure: Diagram of the attack cycle – Huntress
A key concern is that these tokens remain valid even after a password reset, allowing attackers to maintain persistent access.
Offensive Security, Bug Bounty Courses
Legitimate Microsoft Infrastructure Used to Evade Detection
One of the most deceptive aspects of the campaign is its reliance on legitimate Microsoft authentication endpoints.
Victims are directed to the official microsoft.com/devicelogin page, making the process appear entirely legitimate. In this campaign, attackers have further refined the technique by dynamically generating and displaying the device code directly on phishing landing pages.
This removes the need for victims to manually receive or enter codes from emails, streamlining the attack and increasing success rates.

Cloudflare and Railway Infrastructure Central to Campaign
The attack infrastructure heavily leverages trusted cloud services to evade detection.
Nearly all phishing pages are hosted on Cloudflare Workers, taking advantage of the platform’s reputation to bypass web filtering systems. Meanwhile, stolen session tokens are redirected to Railway-hosted infrastructure, which acts as the central credential harvesting engine.
Researchers identified a small cluster of Railway IP addresses responsible for the majority of authentication activity, with a handful of IPs accounting for approximately 84% of observed events.
EvilTokens Phishing-as-a-Service Drives Campaign
Huntress has attributed the activity to a newly emerged phishing-as-a-service platform called EvilTokens, which surfaced on Telegram in early 2026.
The platform offers:
- Automated phishing email distribution
- Spam filter evasion techniques
- Open redirect links for obfuscation
- A centralized dashboard for campaign management
EvilTokens also provides customer support and continuous feature updates, highlighting the increasing professionalization of cybercrime operations.
Advanced Evasion Techniques Complicate Detection
Additional analysis from Palo Alto Networks Unit 42 revealed that the phishing infrastructure incorporates multiple anti-analysis and anti-detection techniques.
These include:
- Disabling right-click and text selection
- Blocking developer tools shortcuts
- Detecting active debugging environments
- Triggering infinite debugger loops
The phishing pages also exfiltrate browser cookies immediately upon loading, further enhancing the attackers’ ability to hijack sessions.
Links to Known Threat Actor Activity
Device code phishing has been increasingly associated with advanced threat groups, including APT29 and Storm-2372, as well as other Russia-aligned actors.
While attribution for this specific campaign remains ongoing, the techniques align with previously documented nation-state and cybercriminal operations.
Mitigation and Defensive Measures
To defend against such attacks, organizations are advised to:
- Monitor sign-in logs for suspicious activity, particularly from Railway IP addresses
- Revoke all refresh tokens for affected accounts
- Block authentication attempts from known malicious infrastructure
- Educate users about device code phishing risks
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Sources: thehackernews.com, huntress.com