Critical GitHub Vulnerability Allowed Remote Code Execution via Single “git push”
A critical security vulnerability affecting GitHub.com and GitHub Enterprise Server has been disclosed, allowing authenticated users to achieve remote code execution (RCE) using a single “git push” command.
Overview of the Vulnerability
The flaw, identified as CVE-2026-3854 with a CVSS score of 8.7, is classified as a command injection issue. It enables attackers with push access to a repository to execute arbitrary commands on the underlying system.
According to GitHub, the issue originated from improper sanitization of user-supplied push option values. These values were incorporated into internal service headers without adequate filtering, creating an opportunity for injection.
Root Cause and Technical Details
At the core of the vulnerability is the handling of metadata within the internal X-Stat header. The header format relies on semicolons as delimiters, which could also be included in user input. This overlap allowed attackers to inject additional metadata fields by crafting malicious push option values.
By chaining multiple injections, researchers demonstrated that it was possible to manipulate the execution environment, bypass sandboxing protections, and ultimately run arbitrary commands on the server.
See Also: So, you want to be a hacker?
Offensive Security, Bug Bounty Courses
Exploitation Method
The attack chain involves three key steps:
- Injecting a non-production rails_env value to bypass sandbox restrictions
- Overriding custom_hooks_dir to redirect the hook directory
- Injecting repo_pre_receive_hooks with a crafted payload to trigger path traversal and command execution
This sequence allowed attackers to execute unsandboxed code as the git user, gaining full control over the affected instance, including file system access and internal configuration visibility.
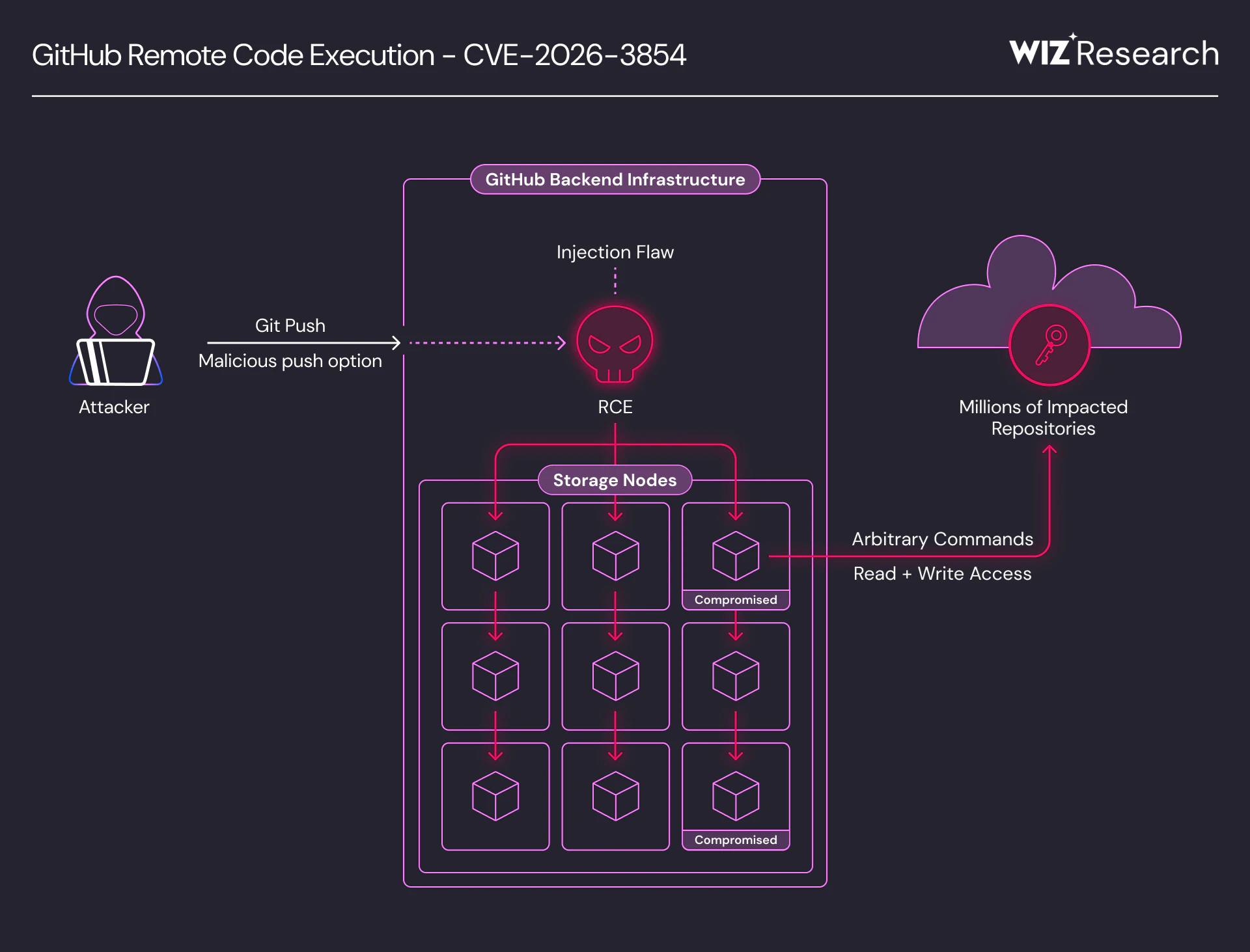
Figure: Vulnerability overview – a single git push compromises GitHub’s internal infrastructure
Discovery and Response
The vulnerability was discovered by cloud security firm Wiz and reported on March 4, 2026. GitHub validated the issue and deployed a fix to GitHub.com within two hours.
Patches have also been released for GitHub Enterprise Server versions 3.14.25, 3.15.20, 3.16.16, 3.17.13, 3.18.8, 3.19.4, 3.20.0, and later. There is currently no evidence that the vulnerability was exploited in the wild.
Impact and Scope
The issue affects multiple GitHub offerings, including GitHub.com, GitHub Enterprise Cloud, and GitHub Enterprise Server.
Due to GitHub’s multi-tenant architecture, successful exploitation on GitHub.com could have led to cross-tenant exposure. This means an attacker might have been able to access repositories belonging to other users or organizations on the same shared infrastructure.
Although certain enterprise-specific features are disabled by default on GitHub.com, researchers demonstrated that these protections could also be bypassed through the same injection technique.
Security Implications
Researchers described the vulnerability as “remarkably easy” to exploit, noting that a large percentage of instances were vulnerable at the time of disclosure.
The incident highlights the risks associated with internal data handling across distributed systems, especially when multiple services rely on shared protocols without strict input validation.
Mitigation and Recommendations
Users of GitHub Enterprise Server are strongly advised to update to the latest patched versions immediately.
Organizations are also encouraged to review how user-controlled input flows through internal systems, particularly when it influences security-sensitive configurations.
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Sources: thehackernews.com, www.wiz.io/blog