Critical nginx-ui Flaw Under Active Exploitation Enables Full Server Takeover

Critical nginx-ui Vulnerability Exploited in the Wild
A newly disclosed critical vulnerability affecting nginx-ui, an open-source web-based management tool for Nginx, is now being actively exploited by threat actors.
Tracked as CVE-2026-33032 with a CVSS score of 9.8, the flaw allows attackers to bypass authentication and gain full control over the Nginx service. The issue, dubbed MCPwn by Pluto Security, exposes a dangerous weakness in the tool’s Model Context Protocol (MCP) integration.
Authentication Bypass Opens Door to Full Server Control
The vulnerability stems from improper security controls applied to two HTTP endpoints: /mcp and /mcp_message.
While the /mcp endpoint enforces authentication and IP allowlisting, the /mcp_message endpoint only relies on IP filtering. Critically, the default configuration treats an empty IP whitelist as “allow all,” effectively exposing the endpoint to any external attacker.
This misconfiguration enables unauthorized users to invoke MCP tools without authentication, allowing them to:
- Restart the Nginx service
- Modify or delete configuration files
- Trigger automatic configuration reloads
In practice, this grants attackers complete control over the web server.
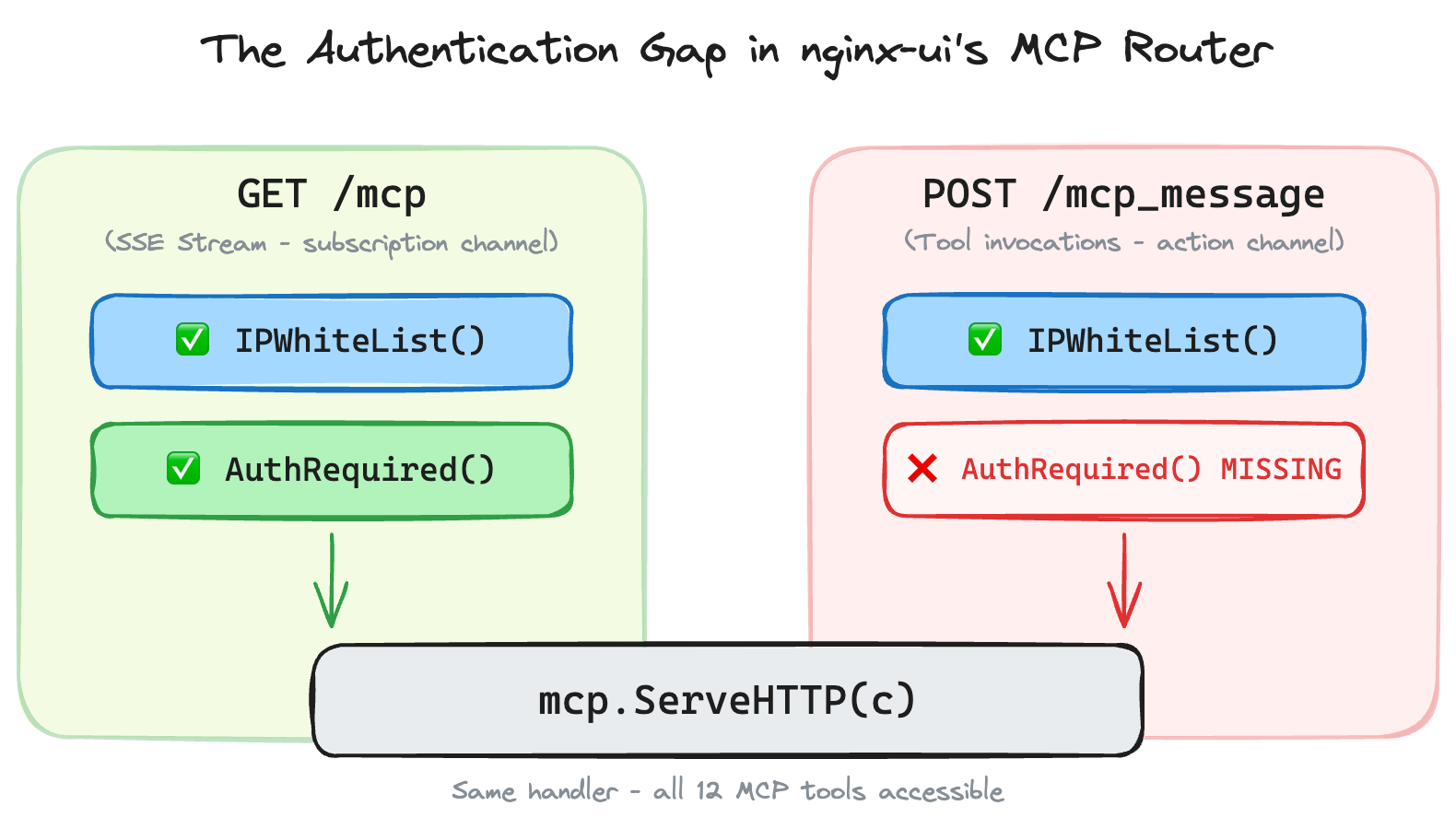
The authentication gap: both endpoints reach the same handler, but only one checks credentials.
Attack Chain Enables Rapid Exploitation
According to researcher Yotam Perkal, exploitation can be completed in seconds using a two-step process:
- Send a GET request to /mcp to establish a session and obtain a session ID
- Send a POST request to /mcp_message using the session ID to execute commands
Although session creation typically requires authentication, attackers can bypass this requirement by chaining a second critical vulnerability.
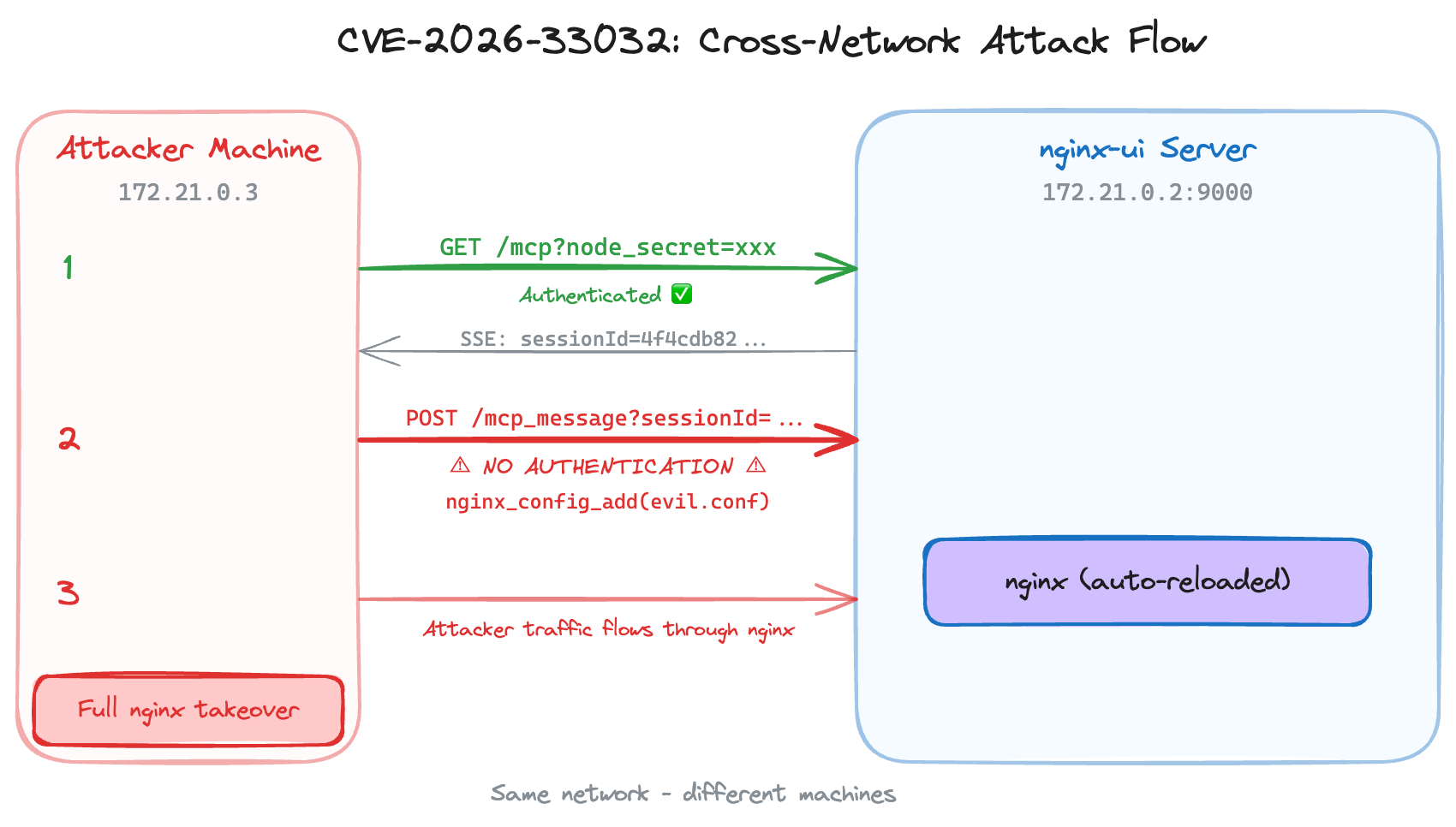
The attack flow: step 1 authenticates to get a session, step 2 uses that session to invoke destructive tools with zero authentication.
Offensive Security, Bug Bounty Courses
Backup Endpoint Flaw Leaks Sensitive Secrets
The attack leverages an additional flaw, CVE-2026-27944, present in versions prior to 2.3.3, which exposes sensitive data through the /api/backup endpoint.
This vulnerability allows unauthenticated attackers to download full system backups, which may contain:
- Credentials
- SSL private keys
- Configuration data
- A critical parameter called node_secret
The extracted node_secret can then be used to authenticate MCP sessions, enabling attackers to fully exploit the authentication bypass in CVE-2026-33032.
Risk of Traffic Interception and Credential Theft
Successful exploitation not only allows configuration tampering but also creates opportunities for deeper compromise.
Attackers could modify Nginx configurations to intercept incoming traffic, inject malicious responses, or harvest administrator credentials. This effectively turns the compromised server into a controlled interception point.
Thousands of Exposed Instances at Immediate Risk
Data from Shodan indicates that approximately 2,600 nginx-ui instances are publicly exposed, with the highest concentrations in China, the United States, Indonesia, Germany, and Hong Kong.
Given the simplicity and speed of exploitation, unpatched systems face immediate risk.
Patch Released, Mitigations Recommended
The vulnerability has been addressed in nginx-ui version 2.3.4, released on March 15, 2026. Organizations are strongly advised to upgrade immediately.
For those unable to patch right away, recommended mitigations include:
- Enforcing authentication on the /mcp_message endpoint
- Changing IP allowlisting behavior from “allow-all” to “deny-all”
- Restricting network access to nginx-ui interfaces
- Disabling MCP functionality where possible
Growing Risks Around MCP Integrations
Researchers warn that integrating MCP functionality into existing applications can introduce significant security risks if not properly secured.
Because MCP endpoints inherit application capabilities without inheriting full security controls, they can unintentionally create powerful backdoors that bypass authentication entirely.
Related MCP Vulnerabilities Highlight Broader Threat
The disclosure comes alongside the identification of additional MCP-related vulnerabilities in Atlassian’s MCP server, dubbed MCPwnfluence.
These flaws, tracked as CVE-2026-27825 and CVE-2026-27826, can be chained to achieve unauthenticated remote code execution within local networks, further underscoring the emerging risks associated with MCP implementations.
As adoption of MCP-based architectures grows, security experts warn that improper implementation could significantly expand the attack surface across enterprise environments.
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Sources: thehackernews.com, pluto.security/blog