Chaos RAT MalwarVariant Distributed via Fake Linux Network Tools

Chaos RAT Returns: New Golang Variant Hits Windows and Linux Systems via Fake Network Tools
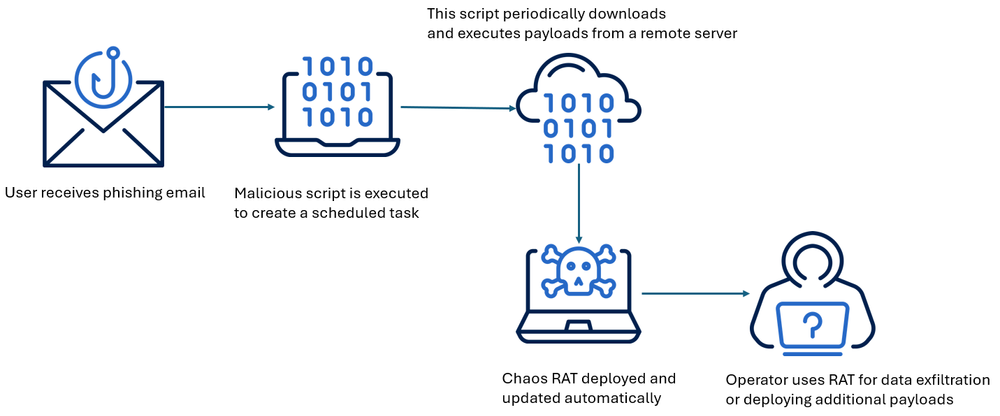
Threat hunters at Acronis have identified an updated variant of the Chaos Remote Access Trojan (RAT) being actively used in attacks targeting both Windows and Linux systems. This latest wave of infections has been linked to phishing campaigns and fake utility downloads, with payloads designed for reconnaissance, remote control, and cryptocurrency mining.
Chaos RAT: A Cross-Platform Golang Trojan
Originally developed in 2017 as an open-source remote administration tool, Chaos RAT gained notoriety in late 2022 when it was deployed in campaigns targeting Linux web servers to drop the XMRig cryptocurrency miner. Written in Go (Golang) and inspired by post-exploitation frameworks like Cobalt Strike and Sliver, Chaos RAT supports:
- Cross-platform compatibility (Windows and Linux)
- A user-friendly administration panel for payload generation and session management
- Full remote control of infected systems
“Chaos RAT provides an administrative panel where users can build payloads, establish sessions, and control compromised machines,” said researchers Santiago Pontiroli, Gabor Molnar, and Kirill Antonenko from Acronis.
Latest Variant (v5.0.3): Advanced Capabilities & Delivery Tactics
The most recent version, Chaos RAT 5.0.3, released on May 31, 2024, has been linked to phishing emails targeting Linux users. Victims are tricked into downloading what appear to be network troubleshooting tools, such as a malicious archive named:
- Connects to a command-and-control (C2) server
- Launches reverse shells
- Exfiltrates system and file information
- Uploads/downloads/deletes files
- Opens arbitrary URLs
- Locks, restarts, or shuts down the system
📌 Persistence Mechanism
On Linux, Chaos RAT maintains persistence by modifying the task scheduler:
See Also: So, you want to be a hacker?
Offensive Security, Bug Bounty Courses
Admin Panel Vulnerabilities Patched (CVE-2024-30850 & CVE-2024-31839)
Interestingly, the Chaos RAT control panel itself was recently found to have two major vulnerabilities:
- CVE-2024-30850: A critical command injection vulnerability (CVSS 8.8) that could allow full server compromise
- CVE-2024-31839: A cross-site scripting (XSS) flaw (CVSS 4.8) that could enable client-side code execution
Both flaws were patched by the tool’s maintainer in May 2024, but their existence underscores the double-edged sword of using publicly available malware platforms.
Targets and Attribution
- Recent malware samples have been uploaded from India in early 2025, suggesting active targeting in South Asian regions.
- Linux variants have been linked to cryptojacking operations, while Chaos RAT appears to be used for initial reconnaissance and post-exploitation control.
- Attribution remains murky, consistent with the nature of open-source malware usage.
“What starts as a developer’s tool can quickly become a threat actor’s instrument of choice,” Acronis researchers noted. “The widespread use of open-source malware muddles attribution and gives APT groups plausible deniability.”
Connected Campaign: Fake Trust Wallet Apps
The resurgence of Chaos RAT coincides with a new malware campaign targeting Trust Wallet users on desktop platforms. The malicious software is spread via:
- Deceptive download links
- Phishing emails
- Bundled software
Once installed, it functions as clipper malware and a credential harvester, capable of:
- Intercepting clipboard data
- Extracting browser-based wallet extensions
- Capturing seed phrases and private keys
“The malware can scan for wallet files, intercept clipboard data, or monitor browser sessions to capture seed phrases or private keys,” said Kedar S. Pandit, researcher at Point Wild.
Trending: OSINT Tool: GoogleDorker
Security Recommendations
For defenders and enterprise security teams:
- Block known C2 domains associated with Chaos RAT
- Monitor
/etc/crontabfor suspicious entries on Linux systems - Use application whitelisting and EDR solutions that detect Golang-based payloads
- Educate users on the risks of downloading software from unverified sources
- Ensure all Chaos RAT admin panels (if used for research or red teaming) are patched
Indicators of Compromise (IOCs):
- NetworkAnalyzer.tar.gz
- Malicious crontab entries referencing remote scripts
- Suspicious outbound connections from
chaos-clientprocesses
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Source: thehackernews.com