Freight Brokers Hit by RMM-Based Cyber Attacks Aimed at Physical Cargo Theft

Threat actors are conducting targeted phishing and social engineering campaigns against freight brokers, carriers, and logistics providers, using malicious links to deploy remote monitoring and management (RMM) tools. Once installed, these tools give attackers full control of victims’ systems, enabling them to hijack cargo shipments, impersonate carriers, and reroute physical goods.
The activity has been ongoing since at least January 2025, with campaigns increasing sharply since August, according to Proofpoint. Nearly two dozen separate operations have been observed — each distributing up to a thousand emails — primarily targeting North American logistics firms, though related attacks were also detected in Brazil, Mexico, India, Germany, Chile, and South Africa.
.jpg) Email response sent to carriers hooked by the load-board lure
Email response sent to carriers hooked by the load-board lure
Source: Proofpoint
Digitized Cargo Theft
Cargo theft — traditionally the physical hijacking or rerouting of trucks and trailers — has evolved into a cyber-physical hybrid crime. Attackers exploit the digital supply-chain layer, using compromised accounts and fake freight listings to deceive carriers and gain remote access to dispatch systems.
Once RMMs like ScreenConnect, PDQ Connect, Fleetdeck, N-able, SimpleHelp, and LogMeIn Resolve are installed, attackers can:
- Control dispatcher systems remotely
- Modify or cancel legitimate bookings
- Block notifications or emails
- Add rogue devices to dispatcher phone extensions
- Book and reroute shipments under the victim carrier’s identity
These manipulations allow attackers to intercept or redirect valuable cargo, such as food, beverages, and electronics, to fraudulent destinations for resale or export.
The National Insurance Crime Bureau (NICB) estimates cargo theft losses in the U.S. exceed $35 billion annually.
Offensive Security, Bug Bounty Courses
Attack Chain
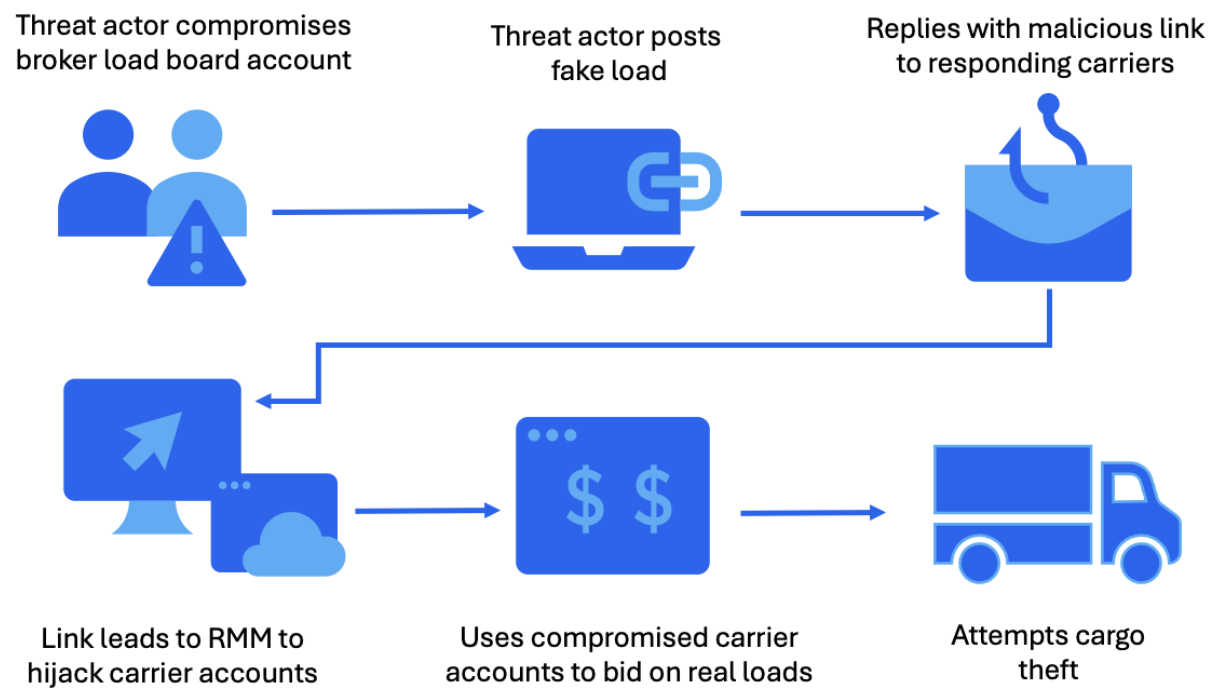 Overview of the attack
Overview of the attack
Source: Proofpoint
Proofpoint researchers describe a well-organized, multi-step attack sequence:
- Initial access – Threat actors use compromised broker or dispatcher email accounts or load board credentials to send phishing emails to logistics firms.
- Social engineering – Messages are highly tailored, mimicking legitimate freight negotiations with urgent requests.
- Payload delivery – Victims are lured to convincing fake sites hosting RMM installers (.exe or .msi), often branded with real carrier logos.
- Execution – Legitimate RMM software is installed, providing remote access. Some attacks chain multiple RMMs — e.g., PDQ Connect installing ScreenConnect and SimpleHelp.
- Post-exploitation – Once access is established, attackers perform system reconnaissance, deploy credential harvesters like WebBrowserPassView, and pivot deeper into corporate environments.
Proofpoint reports that NetSupport, DanaBot, Lumma Stealer, and StealC have also appeared in related activity clusters, suggesting hybrid campaigns involving both data theft and physical cargo diversion.
Real-World Impact
A victim carrier recounted that attackers tricked a dispatcher into installing an RMM, gaining full control of the system. The intruders:
- Deleted booking emails and blocked notifications
- Added their device to the dispatcher’s phone extension
- Used the company’s official FMCSA-registered email and phone to impersonate the business
- Answered verification calls from brokers, hijacking multiple loads
This level of infiltration demonstrates operational knowledge of freight workflows, schedules, and cargo values — suggesting that the campaigns are coordinated with organized crime groups specializing in physical theft.
Trending: Offensive Security Tool: FormPoison
Defensive Measures
To defend against these blended attacks, Proofpoint and other experts recommend:
- Restrict installation of unapproved RMM tools (via endpoint management or group policy).
- Block executable and MSI attachments (.exe / .msi) at email gateways.
- Inspect and sandbox links in emails leading to freight portals or load packets.
- Monitor network traffic for unusual outbound connections from RMM software.
- Implement strict access control for load board and dispatch accounts — enforce MFA and unique credentials.
- Educate logistics staff about fraudulent load listings, urgent negotiation scams, and fake carrier websites.
- Log and audit RMM activity regularly to detect unsanctioned use.
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Source: bleepingcomputer.com