New HybridPetya Ransomware Bypasses UEFI Secure Boot Protection
Discovery of HybridPetya
Researchers at ESET have identified a new ransomware strain dubbed HybridPetya, capable of bypassing UEFI Secure Boot to install a malicious bootkit in the EFI System Partition.
The malware was discovered on VirusTotal, and researchers suggest it may currently be a proof-of-concept (PoC), research project, or early-stage cybercrime tool. While not yet seen in active campaigns, its existence highlights the growing threat of ransomware targeting the UEFI boot process.
Links to Petya and NotPetya
HybridPetya borrows heavily from the infamous Petya and NotPetya malware that caused widespread disruption in 2016 and 2017.
It retains their visual style and attack chain, including bogus BSOD errors and fake CHKDSK messages, while introducing significant new features such as:
- Installation into the EFI System Partition
- Exploitation of CVE-2024-7344 to bypass Secure Boot
- A functional decryption and restoration process for victims who pay
Offensive Security, Bug Bounty Courses
Execution Logic
Once launched, HybridPetya checks if the target system uses UEFI with GPT partitioning. If confirmed, it drops multiple files into the EFI partition, including:
\EFI\Microsoft\Boot\config(encryption keys and victim ID)\EFI\Microsoft\Boot\verify(decryption validation)\EFI\Microsoft\Boot\counter(encryption progress tracker)\EFI\Microsoft\Boot\bootmgfw.efi.old(backup of original bootloader)\EFI\Microsoft\Boot\cloak.dat(XORed bootkit for bypass variant)
The ransomware replaces the original bootloader with the vulnerable reloader.efi and removes \EFI\Boot\bootx64.efi.
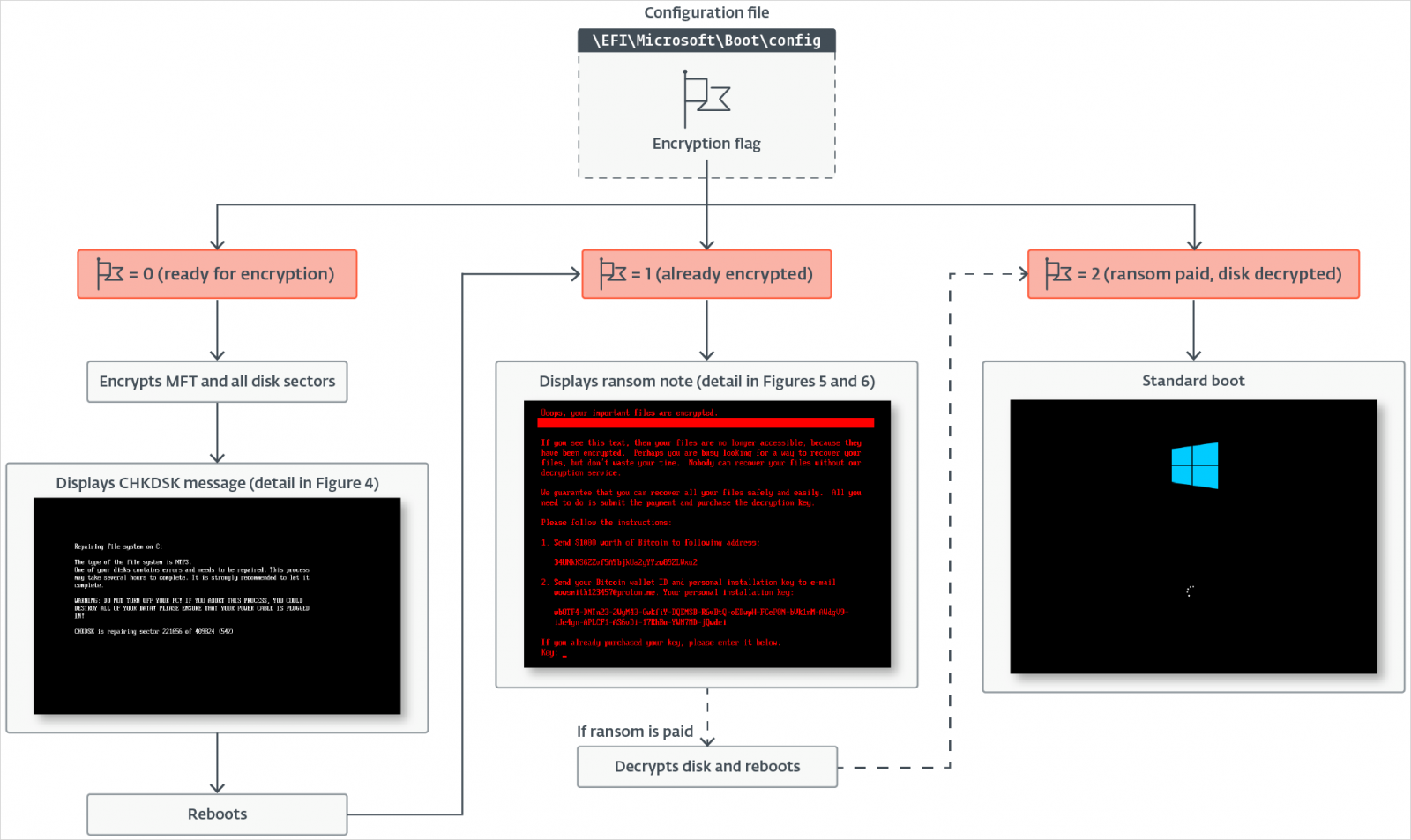 Execution logic
Execution logic
Source: ESET
Victims are then forced into a reboot, triggering encryption of MFT clusters using Salsa20, while a fake CHKDSK screen hides the process.
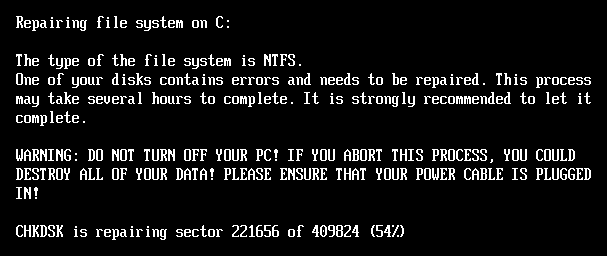 Fake CHKDSK message
Fake CHKDSK message
Source: ESET
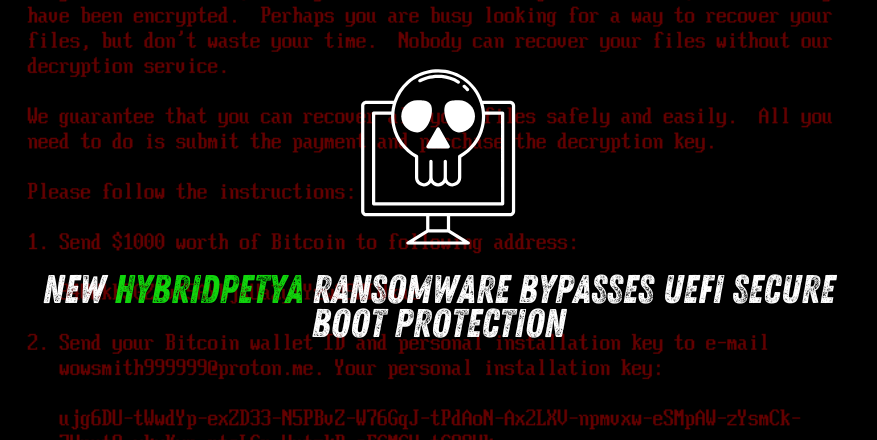
Ransom Demand
After encryption completes, the system reboots again, and victims are shown a ransom note demanding $1,000 in Bitcoin.
The note offers a 32-character key that can be entered to:
- Restore the original bootloader
- Decrypt encrypted clusters
- Reboot the system back to normal operation
Unlike NotPetya, which offered no recovery, HybridPetya includes a functional decryption mechanism, suggesting it is financially motivated.
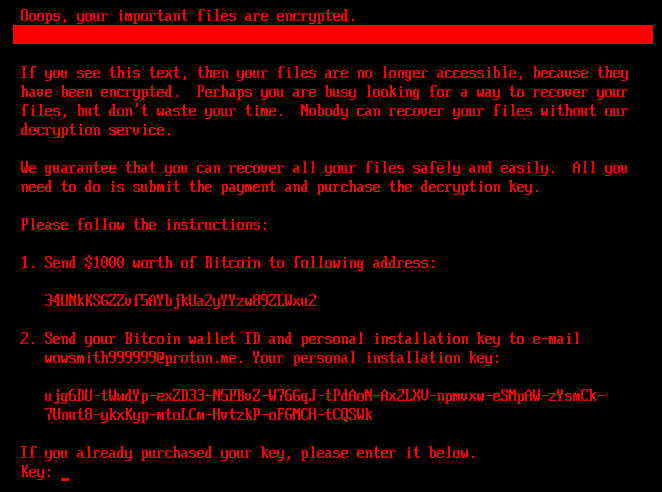 HybridPetya’s ransom note
HybridPetya’s ransom note
Source: ESET
Trending: Offensive Security Tool: FaceDancer
Security Implications
Although no active HybridPetya attacks have been observed, its discovery adds to a growing list of UEFI bootkits with Secure Boot bypass capabilities, including BlackLotus, BootKitty, and Hyper-V Backdoor.
Indicators of compromise (IoCs) have been published on GitHub for defenders.
ESET and Microsoft recommend:
- Applying January 2025 or later Windows updates
- Maintaining offline backups of critical data
- Monitoring systems for suspicious bootloader modifications
Are u a security researcher? Or a company that writes articles about Cyber Security, Offensive Security (related to information security in general) that match with our specific audience and is worth sharing? If you want to express your idea in an article contact us here for a quote: [email protected]
Source: hackread.com